smart card file encryption Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that . Read range is the distance between your phone’s NFC reader to the NFC tag. Average range is between 0-20mm. Tags with a larger antenna may increase the range up to 40mm. Plug and play devices such as NFC readers connected to .
0 · Understanding and Evaluating Virtual S
1 · Understanding Smart Card Authentication
2 · Smart Card Architecture
3 · Personal Identity Verification Card 101
4 · Encrypting and Decrypting Files with Smartcards and PowerShell
5 · Encrypt/Decrypt Files with EFS
$99.99
Encrypting and Decrypting Files with Smartcards and PowerShell. So you want to send a file securely to someone using their smart card certificate, but without using S/MIME? .Non-Repudiation, and Digital Signatures; 2018-11-29. Daily Coding Problem 2
Most of my skill is in Smart Cards, Public Key Infrastructure and Identity .

Encrypting and Decrypting Files with Smartcards and PowerShell. So you want to send a file securely to someone using their smart card certificate, but without using S/MIME? .Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that .
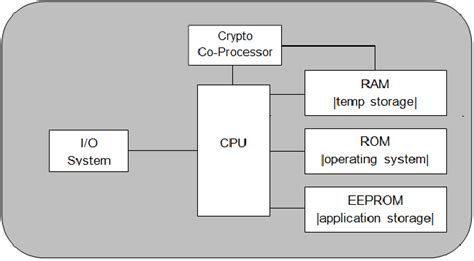
2. A smart card is indeed a complete system on a chip including a microprocessor. Depending on the card, it may have on-die encryption algorithms, storage (up to at 144kB or . Enabling Encrypting File System (EFS) to locate the user's smart card reader from the Local Security Authority (LSA) process in Fast User Switching or in a Remote Desktop .
Understanding and Evaluating Virtual S
This guide provides steps to configure a BitLocker encrypted drive that can be unlocked with a YubiKey 5 series device in Smart Card mode. This will result in a BitLocker .

Virtual smart cards that utilize a TPM provide the three main security principles of traditional smart cards: nonexportability, isolated cryptography, and anti-hammering. Virtual .Encrypt/Decrypt Files with EFS. Microsoft Windows allows the Encryption File System (EFS) feature to use smart card certificates for files and folder encryption. Depending on your smart .
This blog describes the simple, step-by-step process of issuing smart cards or tokens using vSEC:CMS, and then using BitLocker with those cards/tokens. To get started, .
E-mail and PCs are being locked-down with smart cards. Information and entertainment is being delivered via to the home or PC. Home delivery of service is encrypted and decrypted per .
Understanding Smart Card Authentication
Smart cards are one of the efficient devices in providing security in some systems. Smart cards are secured with using encryption algorithms. Finding the best a.
Encrypting and Decrypting Files with Smartcards and PowerShell. So you want to send a file securely to someone using their smart card certificate, but without using S/MIME? .Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that .
2. A smart card is indeed a complete system on a chip including a microprocessor. Depending on the card, it may have on-die encryption algorithms, storage (up to at 144kB or . Enabling Encrypting File System (EFS) to locate the user's smart card reader from the Local Security Authority (LSA) process in Fast User Switching or in a Remote Desktop .
This guide provides steps to configure a BitLocker encrypted drive that can be unlocked with a YubiKey 5 series device in Smart Card mode. This will result in a BitLocker . Virtual smart cards that utilize a TPM provide the three main security principles of traditional smart cards: nonexportability, isolated cryptography, and anti-hammering. Virtual .
Encrypt/Decrypt Files with EFS. Microsoft Windows allows the Encryption File System (EFS) feature to use smart card certificates for files and folder encryption. Depending on your smart . This blog describes the simple, step-by-step process of issuing smart cards or tokens using vSEC:CMS, and then using BitLocker with those cards/tokens. To get started, .E-mail and PCs are being locked-down with smart cards. Information and entertainment is being delivered via to the home or PC. Home delivery of service is encrypted and decrypted per .
Smart Card Architecture
auburn police radio frequency
auburn maine radio stations
$11.99
smart card file encryption|Personal Identity Verification Card 101