rfid key card hack Using the exploit requires a genuine MIFARE Classic keycard – active or expired – and any device that can write data to a card. Some examples of devices that can hack an NFC card include . Get live coverage of SEC college football games with home and away feeds for every team on SiriusXM, including the Auburn Tigers. Hear exclusive interviews with Auburn players and coaches, plus expert analysis and news from the top .Fans can listen to free, live streaming audio of Auburn Sports Network radio broadcasts of Tiger games and coach's shows. Computer; Mobile App; Radio; TuneIn Opens in a new window ; Audio.
0 · rfid scammers
1 · rfid scam
2 · rfid how to block
3 · rfid hack tool
4 · is rfid safe to hack
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid signal
A total of 14 teams make it into the playoffs. The 14-team field consists of seven teams from the AFC and seven teams from the NFC. There are four division winners and three Wild Card .
The technique is a collection of security vulnerabilities that would allow a hacker to almost instantly open several models of Saflok-brand RFID-based keycard locks sold by the Swiss lock maker. Card keys are the most obvious use, but the tricks don’t stop there: the Chameleon can also be used to attack RFID readers by executing an MFKey32 attack. You can also use it . Using the exploit requires a genuine MIFARE Classic keycard – active or expired – and any device that can write data to a card. Some examples of devices that can hack an NFC card include . The technique is a collection of security vulnerabilities that would allow a hacker to almost instantly open several models of Saflok-brand RFID-based keycard locks sold by the Swiss lock maker.
Card keys are the most obvious use, but the tricks don’t stop there: the Chameleon can also be used to attack RFID readers by executing an MFKey32 attack. You can also use it to sniff for keys. Using the exploit requires a genuine MIFARE Classic keycard – active or expired – and any device that can write data to a card. Some examples of devices that can hack an NFC card include .
Step-by-Step Tutorial: How to Copy or Clone Access Cards and Key Fobs. Access credentials are prone to hacking. This post explains how easy it is to copy access cards with Flipper Zero, off-the-shelf hardware, and an app. 10 min reading time. It took one whole search and at the low low cost of [10 dollars] (https://www.ebay.com/bhp/rfid-copier) and less than a minute of their time they can copy a 125kHz card. There are even instructions for 13.6mHz cards capable of NFC as well as interpreting read outs for both in the blog I'm on.

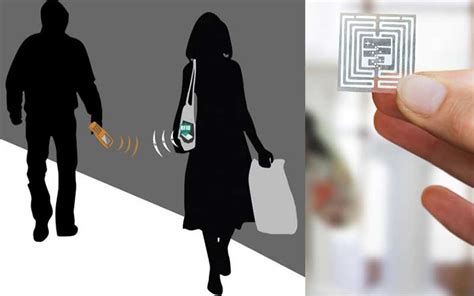
Common RFID hacking techniques include RFID signal interception, tag cloning, replay attacks, brute-forcing cryptographic keys, signal jamming, and exploiting weak encryption or authentication mechanisms. Researchers found—and helped fix—a flaw in Vingcard RFID locks that would let hackers break into any room in hotels around the world. Security researchers Ian Carroll and Lennert Wouters discovered a technique that would allow a hacker to almost instantly unlock certain models of Saflok-brand RFID-based keycard locks,.
The technique is a collection of security vulnerabilities that would allow a hacker to almost instantly open several models of Saflok-brand RFID-based keycard locks sold by the Swiss lock maker Dormakaba. The Saflok systems are installed on 3 million doors worldwide, inside 13,000 properties in 131 countries. Cybersecurity researchers have uncovered a hardware backdoor within a particular model of MIFARE Classic contactless cards that could allow authentication with an unknown key and open hotel rooms and office doors. The technique is a collection of security vulnerabilities that would allow a hacker to almost instantly open several models of Saflok-brand RFID-based keycard locks sold by the Swiss lock maker.
Card keys are the most obvious use, but the tricks don’t stop there: the Chameleon can also be used to attack RFID readers by executing an MFKey32 attack. You can also use it to sniff for keys. Using the exploit requires a genuine MIFARE Classic keycard – active or expired – and any device that can write data to a card. Some examples of devices that can hack an NFC card include .

Step-by-Step Tutorial: How to Copy or Clone Access Cards and Key Fobs. Access credentials are prone to hacking. This post explains how easy it is to copy access cards with Flipper Zero, off-the-shelf hardware, and an app. 10 min reading time.
It took one whole search and at the low low cost of [10 dollars] (https://www.ebay.com/bhp/rfid-copier) and less than a minute of their time they can copy a 125kHz card. There are even instructions for 13.6mHz cards capable of NFC as well as interpreting read outs for both in the blog I'm on. Common RFID hacking techniques include RFID signal interception, tag cloning, replay attacks, brute-forcing cryptographic keys, signal jamming, and exploiting weak encryption or authentication mechanisms. Researchers found—and helped fix—a flaw in Vingcard RFID locks that would let hackers break into any room in hotels around the world.
rfid scammers
Security researchers Ian Carroll and Lennert Wouters discovered a technique that would allow a hacker to almost instantly unlock certain models of Saflok-brand RFID-based keycard locks,.
The technique is a collection of security vulnerabilities that would allow a hacker to almost instantly open several models of Saflok-brand RFID-based keycard locks sold by the Swiss lock maker Dormakaba. The Saflok systems are installed on 3 million doors worldwide, inside 13,000 properties in 131 countries.
rfid scam
$2.85
rfid key card hack|rfid scam