hack any rfid card The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Popular 125 kHz protocols: EM-Marin, HID Prox II, and . नावभक 1य ईंधन सम्मिश्र/NUCLEAR FUEL COMPLEX प्रशासन/ ADMINISTRATION (आईएसओ ,1009, 90001 औ 45001 संगठन An ISO 9001, 14001 & 45001 Organization) द 3रभाष/Phone: 040 .
0 · rfid scammers
1 · rfid scam
2 · rfid how to block
3 · rfid hack tool
4 · is rfid safe to hack
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid signal
Custom On-Metal NFC Plastic Sticker. Custom NFC tags are created at the .
What can it do? The ChameleonMini can extract info from card keys and key fobs, including cloning the UID and storing the data for later. Card keys are the most obvious use, . The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Popular 125 kHz protocols: EM-Marin, HID Prox II, and .
What can it do? The ChameleonMini can extract info from card keys and key fobs, including cloning the UID and storing the data for later. Card keys are the most obvious use, but the tricks don’t. The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Popular 125 kHz protocols: EM-Marin, HID Prox II, and Indala.
The technique is a collection of security vulnerabilities that would allow a hacker to almost instantly open several models of Saflok-brand RFID-based keycard locks sold by the Swiss lock maker. Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here! Some public transit cards can be hacked to get free transit, but most systems are secured against this sort of thing. I've seen a public transit system that uses Mifare Classic 1k cards to store the dollar value in the card. Radio Frequency Identification (RFID), is a technology that uses electromagnetic fields to automatically identify and/or track “tags” that contain electronically stored information. Some tags are passive, therefore they are activated by the electromagnetic fields generated by nearby readers.
One Time Write RFID tag, the best for duplicating Mifare Classic. In this video you will discover how to bypass an RFID reader by working directly on the door.
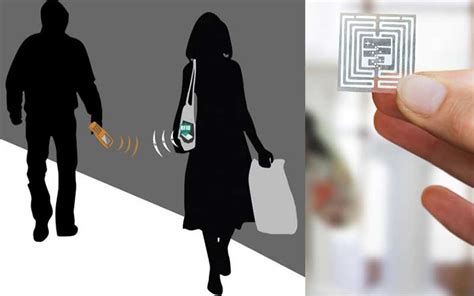
Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.
The first attack on Mifare cards is called Darkside attack, which exploit the weak pseudo-random generator on the card to discover a single key. This attack aims to recover one key from the. Most of the attacks discovered against contactless payments work on top of the relay attack. The identified security issues result from flawed implementation of the standard. Others stem from failure of the issuer and the terminal to validate EMV transactions which is highly flexible in terms of card authentication modes, cardholder . What can it do? The ChameleonMini can extract info from card keys and key fobs, including cloning the UID and storing the data for later. Card keys are the most obvious use, but the tricks don’t. The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Popular 125 kHz protocols: EM-Marin, HID Prox II, and Indala.
The technique is a collection of security vulnerabilities that would allow a hacker to almost instantly open several models of Saflok-brand RFID-based keycard locks sold by the Swiss lock maker. Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here! Some public transit cards can be hacked to get free transit, but most systems are secured against this sort of thing. I've seen a public transit system that uses Mifare Classic 1k cards to store the dollar value in the card. Radio Frequency Identification (RFID), is a technology that uses electromagnetic fields to automatically identify and/or track “tags” that contain electronically stored information. Some tags are passive, therefore they are activated by the electromagnetic fields generated by nearby readers.
One Time Write RFID tag, the best for duplicating Mifare Classic. In this video you will discover how to bypass an RFID reader by working directly on the door. Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking. The first attack on Mifare cards is called Darkside attack, which exploit the weak pseudo-random generator on the card to discover a single key. This attack aims to recover one key from the.

rfid scammers
rfid scam

rfid how to block
rfid hack tool
is rfid safe to hack
I have a Proxmark3 easy and would just like to read an NFC tag from my cell .Date: October 18, 2018 Author: Salvador Mendoza 0 Comments. Intro. The new version of Proxmark3 family (RDV4) contains special features which might .
hack any rfid card|rfid hack tool