information read on silent mode for the rfid system With session 2 or 3 after the tags are read, they remain silent for at least two seconds after the reader stops transmitting, allowing other, weaker tags to be heard. Summary The number of RFID configurations can be bewildering, but the following guidelines will get your application going in the right direction:
Using an NFC Reader/Writer accessory you can use amiibo on your Nintendo 3DS or Nintendo 2DS. Learn more in this video.Official site: https://www.nintend.
0 · tuning rfid settings
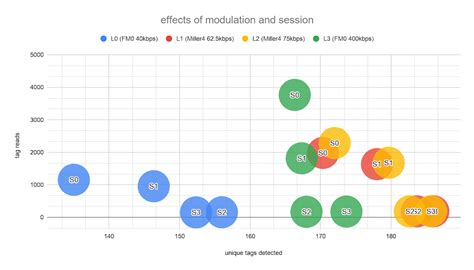
1 · tuning rfid configuration in session
2 · session 0 rfid
3 · rfid settings explained
4 · rfid session settings
NFC basics. This document describes the basic NFC tasks you perform in Android. It explains how to send and receive NFC data in the form of NDEF messages and describes the Android framework APIs that support .

In 2007, the Danish Company RFIDsec developed a passive RFID with privacy enhancing technologies built-in including built-in firewall access controls, communication encryption and a . silent mode ensuring that the consumer at point of sales can get exclusive control of the key to . Radio Frequency Identification (RFID) technology uses radio waves to identify .In 2007, the Danish Company RFIDsec developed a passive RFID with privacy enhancing technologies built-in including built-in firewall access controls, communication encryption and a . silent mode ensuring that the consumer at point of sales can get exclusive control of the key to . control the RFID.
Radio Frequency Identification (RFID) technology uses radio waves to identify virtually anything. It is a wireless system consisting of an RFID tag and an RFID reader. RFID tags store data that can be read, even from a distance-- without making any physical contact or requiring a line of sight.The process of identifying an asset using RFID involves three main components – the tag itself, a reader or scanner device, and a database or software system for storing and managing data. The first step is encoding information on to each unique tag before attaching it to an asset. With session 2 or 3 after the tags are read, they remain silent for at least two seconds after the reader stops transmitting, allowing other, weaker tags to be heard. Summary The number of RFID configurations can be bewildering, but the following guidelines will get your application going in the right direction:
Impinj Protected Mode, a security and privacy feature exclusive to Impinj chips, ensures that a RAIN RFID tag remains silent, making it effectively invisible, unless a reader first provides an 8-character PIN.All information on RFID tags, such as product attributes, physical dimensions, prices or laundering requirements can be scanned wirelessly by a reader at high speed and from a distance of several metres.
Using radio waves, RFID can write, store and transmit information without requiring line-of-sight scanning. Easily reading data from RFID tags allows you to identify single items or entire batches of goods simultaneously.Personal RFID devices – found, e.g., in access cards and contactless credit cards – are vulnerable to unauthorized reading, owner tracking and different types of relay attacks. We observe that accessing a personal RFID device fundamentally requires moving. Guidelines for Securing Radio Frequency Identification (RFID) Systems. Published. April 6, 2007. Author (s) Tom T. Karygiannis, Bernard Eydt, Greg Barber, Lynn Bunn, T. Phillips. Abstract. This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks.
tuning rfid settings
RFID (radio frequency identification) is a form of wireless communication that incorporates the use of electromagnetic or electrostatic coupling in the radio frequency portion of the electromagnetic spectrum to uniquely identify an object, animal or person.In 2007, the Danish Company RFIDsec developed a passive RFID with privacy enhancing technologies built-in including built-in firewall access controls, communication encryption and a . silent mode ensuring that the consumer at point of sales can get exclusive control of the key to . control the RFID. Radio Frequency Identification (RFID) technology uses radio waves to identify virtually anything. It is a wireless system consisting of an RFID tag and an RFID reader. RFID tags store data that can be read, even from a distance-- without making any physical contact or requiring a line of sight.The process of identifying an asset using RFID involves three main components – the tag itself, a reader or scanner device, and a database or software system for storing and managing data. The first step is encoding information on to each unique tag before attaching it to an asset.
With session 2 or 3 after the tags are read, they remain silent for at least two seconds after the reader stops transmitting, allowing other, weaker tags to be heard. Summary The number of RFID configurations can be bewildering, but the following guidelines will get your application going in the right direction: Impinj Protected Mode, a security and privacy feature exclusive to Impinj chips, ensures that a RAIN RFID tag remains silent, making it effectively invisible, unless a reader first provides an 8-character PIN.
All information on RFID tags, such as product attributes, physical dimensions, prices or laundering requirements can be scanned wirelessly by a reader at high speed and from a distance of several metres.
Using radio waves, RFID can write, store and transmit information without requiring line-of-sight scanning. Easily reading data from RFID tags allows you to identify single items or entire batches of goods simultaneously.Personal RFID devices – found, e.g., in access cards and contactless credit cards – are vulnerable to unauthorized reading, owner tracking and different types of relay attacks. We observe that accessing a personal RFID device fundamentally requires moving. Guidelines for Securing Radio Frequency Identification (RFID) Systems. Published. April 6, 2007. Author (s) Tom T. Karygiannis, Bernard Eydt, Greg Barber, Lynn Bunn, T. Phillips. Abstract. This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks.
tuning rfid configuration in session
is the capital one contactless card rfid
hsbc basic bank account debit card contactless
An Android NFC app for reading, writing, analyzing, etc. MIFARE Classic RFID .
information read on silent mode for the rfid system|rfid session settings